- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
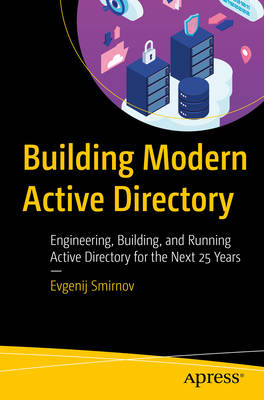
Building Modern Active Directory
Engineering, Building, and Running Active Directory for the Next 25 Years
Evgenij SmirnovDescription
Break the vicious circle of designs perpetuating the errors of the past and "just click next and accept the defaults" implementations preventing a secure and reliable future. This book looks at the typical patterns and antipatterns in Active Directory (AD) design, deployment, and operations and provides an approach to building and operating AD that is based on engineering (analyzing and fulfilling requirements) rather than design (formulating requirements).
The book starts with an historical overview of AD and its future 25 years later. You then learn about the challenges that organizations running AD are facing today followed by understanding how to avoid them while learning modern requirements for more efficient and effective AD performance. After that, you go through business requirements influencing the AD topology along with ways to engineer information lookup to protect high-value objects. The book looks at two main protocols and the many dialects that AD offers to engineer an authentication service that fulfills modern requirements while leaving insecure legacy configurations behind. Managing AD from both the security and usability perspectives is discussed next in the book. Building, operating, and transitioning to a modern AD is demonstrated in detail. The book guides you with the next steps of your journey to achieve a secure and reliable AD.
After reading this book, you will be able to bridge the gap between the two approaches by analyzing real-world business requirements, explaining the decision-making process in both design and engineering, and ultimately providing concrete engineering guidelines for typical implementation scenarios.
What Will You Learn
- Build a modern Active Directory (AD), leaving behind design antipatterns that are not valid anymore
- Build a "secure by design" AD and accommodate legacy technology without compromising the overall security
- Understand advanced AD functionality such as controlling object visibility and partitioning Kerberos authentication by Authentication Policies
- Operate a modern AD, react to changing business requirements, and respond to ever-evolving security threats
Who This Book Is For
Active Directory (AD) architects and consultants who need to provide design and engineering advice to customers; AD administrators tasked with modernizing and securing AD in their organizations; security architects wishing to learn the AD design patterns to watch out for
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 497
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9798868809408
- Date de parution :
- 21-11-24
- Format:
- Livre broché
- Format numérique:
- Trade paperback (VS)
- Dimensions :
- 156 mm x 234 mm
- Poids :
- 743 g