- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
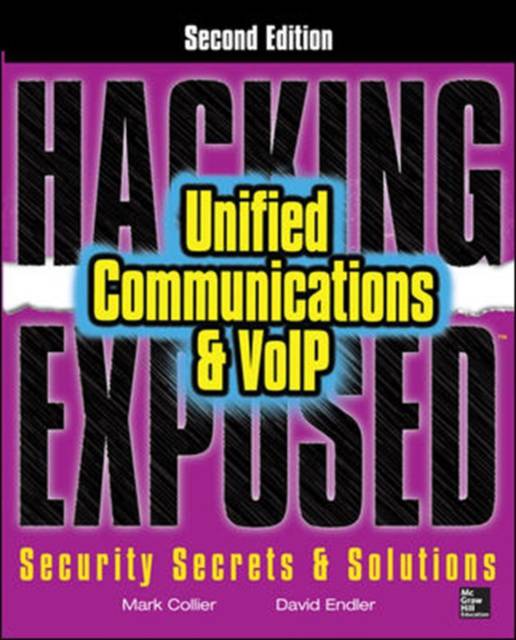
Hacking Exposed Unified Communications & Voip Security Secrets & Solutions, Second Edition
Mark Collier, David Endler
Livre broché | Anglais
76,95 €
+ 153 points
Description
The latest techniques for averting UC disaster
Establish a holistic security stance by learning to view your unified communications infrastructure through the eyes of the nefarious cyber-criminal. Hacking Exposed Unified Communications & VoIP, Second Edition offers thoroughly expanded coverage of today's rampant threats alongside ready-to deploy countermeasures. Find out how to block TDoS, toll fraud, voice SPAM, voice social engineering and phishing, eavesdropping, and man-in-the-middle exploits. This comprehensive guide features all-new chapters, case studies, and examples.
- See how hackers target vulnerable UC devices and entire networks
- Defend against TDoS, toll fraud, and service abuse
- Block calling number hacks and calling number spoofing
- Thwart voice social engineering and phishing exploits
- Employ voice spam mitigation products and filters
- Fortify Cisco Unified Communications Manager
- Use encryption to prevent eavesdropping and MITM attacks
- Avoid injection of malicious audio, video, and media files
- Use fuzzers to test and buttress your VoIP applications
- Learn about emerging technologies such as Microsoft Lync, OTT UC, other forms of UC, and cloud and WebRTC
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 560
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9780071798761
- Date de parution :
- 16-12-13
- Format:
- Livre broché
- Format numérique:
- Trade paperback (VS)
- Dimensions :
- 186 mm x 234 mm
- Poids :
- 925 g