En raison d'une grêve chez bpost, votre commande pourrait être retardée. Vous avez besoin d’un livre rapidement ? Nos magasins vous accueillent à bras ouverts !
- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
En raison de la grêve chez bpost, votre commande pourrait être retardée. Vous avez besoin d’un livre rapidement ? Nos magasins vous accueillent à bras ouverts !
- Retrait gratuit dans votre magasin Club
- 7.000.0000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
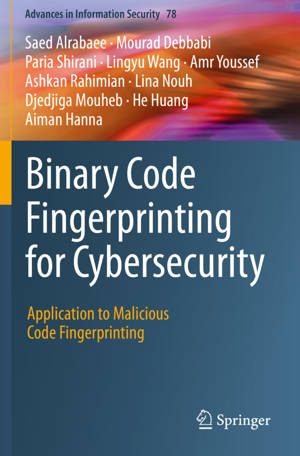
Binary Code Fingerprinting for Cybersecurity
Application to Malicious Code Fingerprinting
Saed Alrabaee, Mourad Debbabi, Paria Shirani, Lingyu Wang, Amr Youssef, Ashkan Rahimian, Lina Nouh, Djedjiga Mouheb, He Huang, Aiman Hanna
158,45 €
+ 316 points
Format
Description
This book addresses automated software fingerprinting in binary code, especially for cybersecurity applications. The reader will gain a thorough understanding of binary code analysis and several software fingerprinting techniques for cybersecurity applications, such as malware detection, vulnerability analysis, and digital forensics. More specifically, it starts with an overview of binary code analysis and its challenges, and then discusses the existing state-of-the-art approaches and their cybersecurity applications. Furthermore, it discusses and details a set of practical techniques for compiler provenance extraction, library function identification, function fingerprinting, code reuse detection, free open-source software identification, vulnerability search, and authorship attribution. It also illustrates several case studies to demonstrate the efficiency, scalability and accuracy of the above-mentioned proposed techniques and tools.
This book also introduces several innovative quantitative and qualitative techniques that synergistically leverage machine learning, program analysis, and software engineering methods to solve binary code fingerprinting problems, which are highly relevant to cybersecurity and digital forensics applications. The above-mentioned techniques are cautiously designed to gain satisfactory levels of efficiency and accuracy.
Researchers working in academia, industry and governmental agencies focusing on Cybersecurity will want to purchase this book. Software engineers and advanced-level students studying computer science, computer engineering and software engineering will also want to purchase this book.
This book also introduces several innovative quantitative and qualitative techniques that synergistically leverage machine learning, program analysis, and software engineering methods to solve binary code fingerprinting problems, which are highly relevant to cybersecurity and digital forensics applications. The above-mentioned techniques are cautiously designed to gain satisfactory levels of efficiency and accuracy.
Researchers working in academia, industry and governmental agencies focusing on Cybersecurity will want to purchase this book. Software engineers and advanced-level students studying computer science, computer engineering and software engineering will also want to purchase this book.
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 249
- Langue:
- Anglais
- Collection :
- Tome:
- n° 78
Caractéristiques
- EAN:
- 9783030342401
- Date de parution :
- 01-03-21
- Format:
- Livre broché
- Format numérique:
- Trade paperback (VS)
- Dimensions :
- 156 mm x 234 mm
- Poids :
- 385 g
Les avis
Nous publions uniquement les avis qui respectent les conditions requises. Consultez nos conditions pour les avis.