- Retrait gratuit dans votre magasin Club
- 7.000.000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
- Retrait gratuit dans votre magasin Club
- 7.000.0000 titres dans notre catalogue
- Payer en toute sécurité
- Toujours un magasin près de chez vous
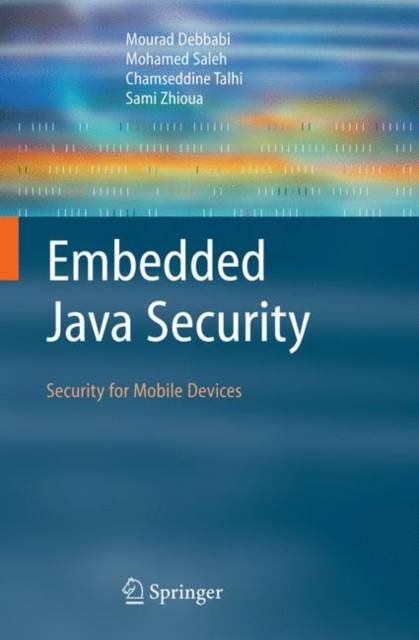
Embedded Java Security
Security for Mobile Devices
Mourad Debbabi, Mohamed Saleh, Chamseddine Talhi, Sami ZhiouaDescription
Java brings more functionality and versatility to the world of mobile devices, but it also introduces new security threats. This book is a comprehensive presentation of embedded Java security. No other book specifically addresses the topic of embedded Java security. The main components of embedded Java are also generally presented to give an idea about the platform architecture. To assess the effectiveness of the security model, an evaluation of the security features is carried out with results presented in the framework of the MEHARI method for risk analysis, and the Common Criteria methodology of security evaluation. The usefulness of this security evaluation is to point out areas that need security hardening. This book provides researchers and practitioners alike with a broader and deeper understanding of the issues involved in embedded Java security, and - as a larger view - mobile devices security.
Spécifications
Parties prenantes
- Auteur(s) :
- Editeur:
Contenu
- Nombre de pages :
- 246
- Langue:
- Anglais
Caractéristiques
- EAN:
- 9781849966238
- Date de parution :
- 13-10-10
- Format:
- Livre broché
- Format numérique:
- Trade paperback (VS)
- Dimensions :
- 234 mm x 156 mm
- Poids :
- 367 g
Les avis
Nous publions uniquement les avis qui respectent les conditions requises. Consultez nos conditions pour les avis.